HackTheBox Sherlocks - OpTinselTrace-1
Scenario
An elf named "Elfin" has been acting rather suspiciously lately. He's been working at odd hours and seems to be bypassing some of Santa's security protocols. Santa's network of intelligence elves has told Santa that the Grinch got a little bit too tipsy on egg nog and made mention of an insider elf! Santa is very busy with his naughty and nice list, so he’s put you in charge of figuring this one out. Please audit Elfin’s workstation and email communications. Please note - these Sherlocks are built to be completed sequentially and in order!
Evidence Handling
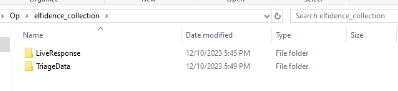
In this sherlock, we are provided with 2 types of evidence which are the Triage data and live response from the workstation when collection tool was ran. (KAPE)
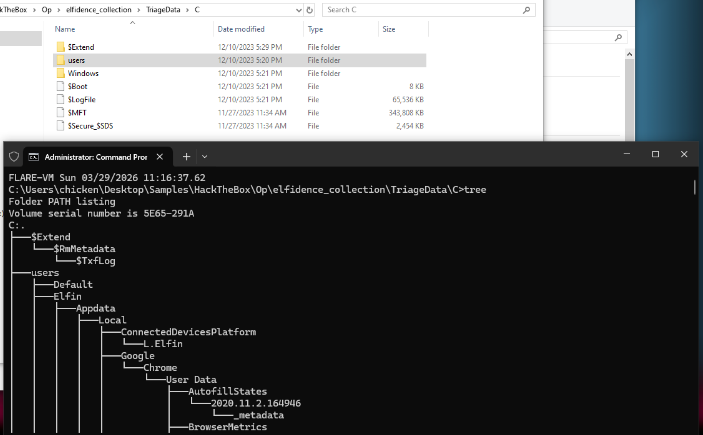
Inside the TriageData, we have quite a lot of artifacts that can be used to aid our investigate and it is quite generous of the author of this sherlock to leave MFT and USN Journal here as they can be very powerful to determine file operation on that Windows system in quite recent time
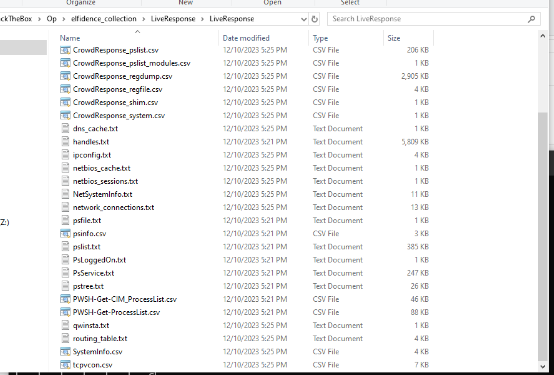
Meanwhile inside LiveResponse folder, we can see that we have process information including its network connection when the collection tool was used so this might come in handy to identidy suspicious process and network activity as well.
Now let's start the investigation
Investigation
Task 1: What is the name of the email client that Elfin is using?
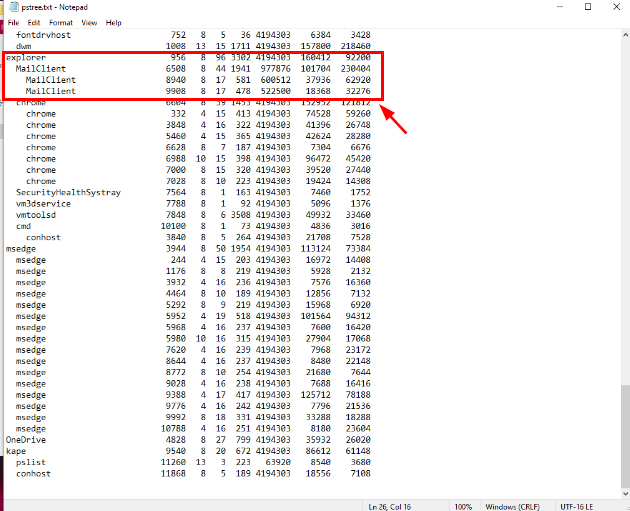
The scenario strongly suggest that the user Elfin is potentially be an insider threat so normally I would go to for UserAsset registry key, and JumpLists to find the latest file and executable ran by this user but this time, I open the pstree.txt from LiveResponse folder which I can see that there is MailClient.exe which is a process belong to eM Client running under explorer.exe and that's basically mean it was running by user (Elfin).
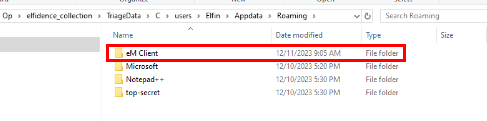
And by inspecting AppData\Roaming folder of Elfin user, we can see eMClient folder which contains files associated to eM Client, a email client used by Elfin user.
eM Client
Task 2: What is the email the threat actor is using?
There are 2 main ways to solve this sherlock:
- First: Open each SQLite3 dabase that stores email messages
- Second: Download eM Client, replace whole AppData\Roaming and open it which should let us read all email in eM Client (more user friendly this way)
I will go with the second approach as it is more UI friendly for me to read and capture screenshot to put in this write-up.
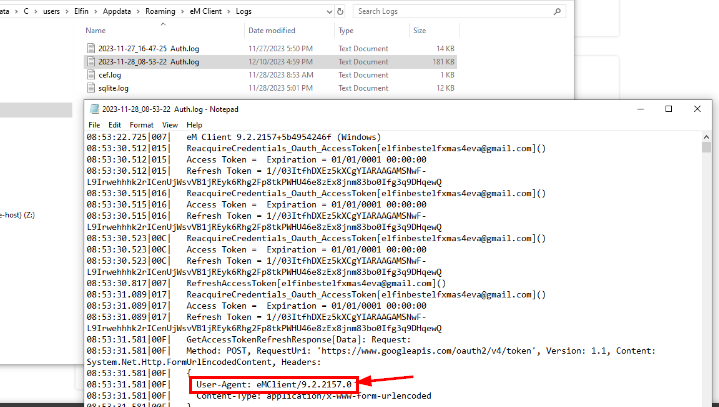
First, I want to download the exact version of eM Client that Elfin user used so I opened one of the log files located inside Logs folder and we can see that on the user-agent, it is reveals that eM Client version installed on this workstation is 9.2.2157.0
With that information, we can now go to eM Client download for Windows and I don't want to download the latest version, I want old version so we can click "release history" to download old version of eM Client.
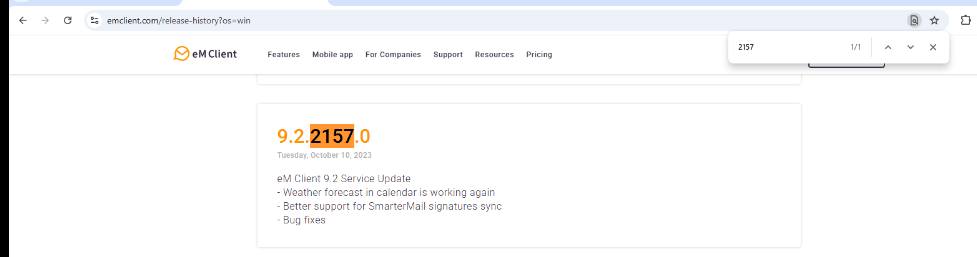
Inside this release history page, we can search for the specific version we want to download the installer and then install it.
After finishing the installation, replace C:\Users\username\AppData\Roaming\eM Client with the artifacts we have (entire folder)
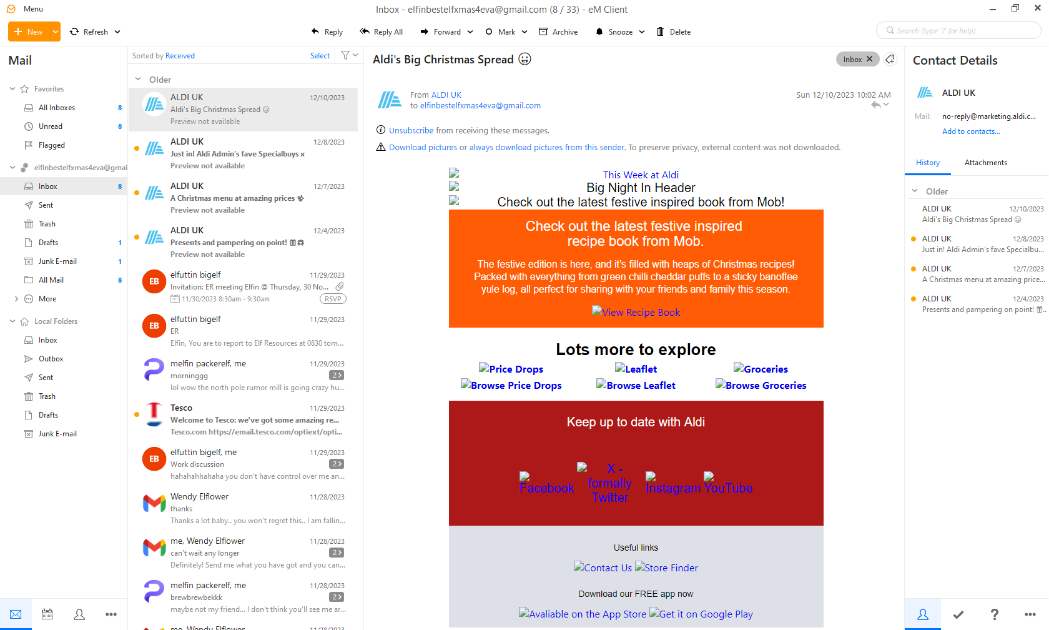
Now when we open eM client, we should be able to read every email saved in SQLite3 database from Elfin workstation.
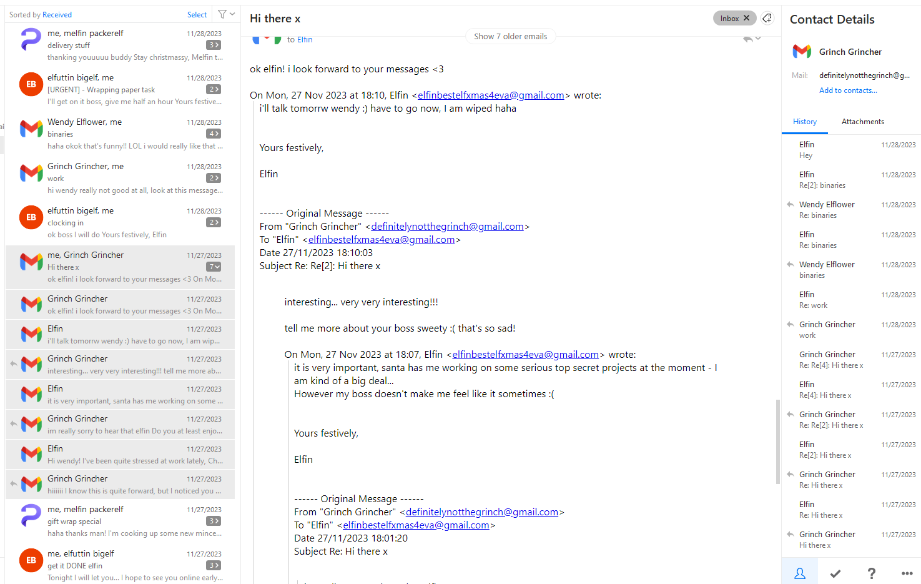
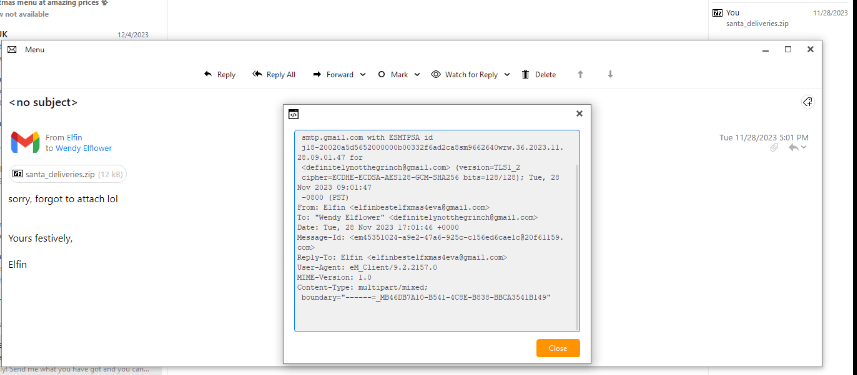
I started digging into each email to gather the context around Elfin circle, and we can see that Elfin was using "elfinbestelfxmas4eva@gmail.com" and he had a conversation with "Grinch Grincher" (definitelynotthegrinch@gmail) about some top secrets project and Elfin's boss.
Elfin even told "Grinch Grincher" that he has accessed to santas special binaries.
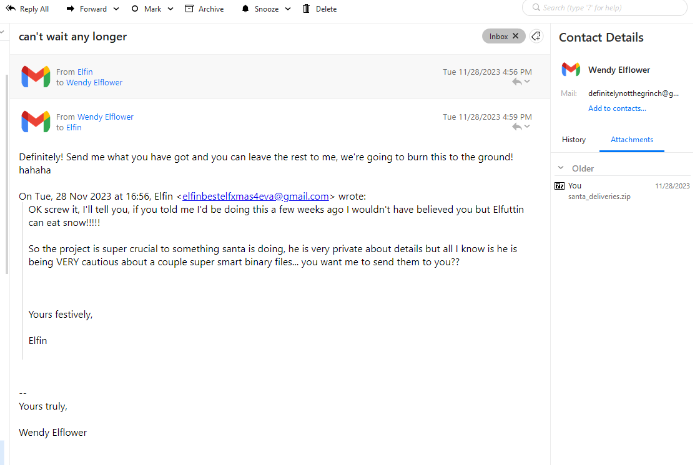
And look like Elfin ended up sending it to "Grinch Grincher" as well, it seem like Elfin was pissing off about his boss, Elfuttin so he offered "Grinch Grincher" the binary and even sent it to him.
This is confirmed that whoever using "definitelynotthegrinch@gmail" is the threat actor which use social engineering tactic to Elfin and eventually got what they want.
I also noticed that the name was changed to "Wendy Elflower" as well
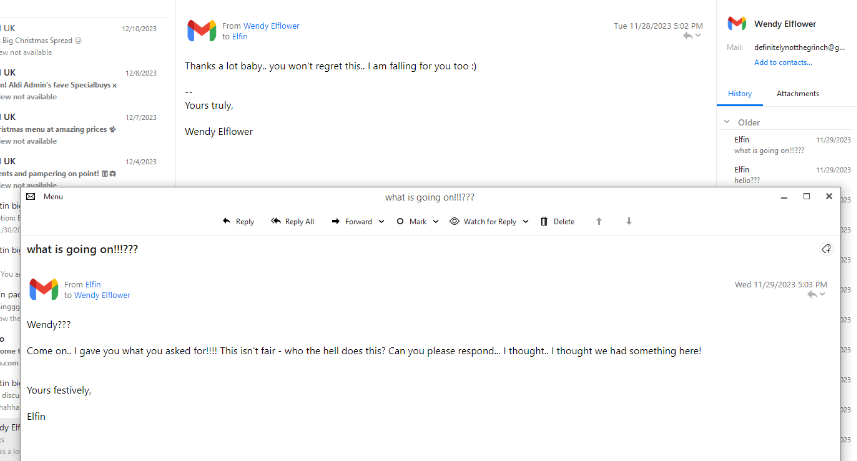
After Elfin sent the binary in zip file, the threat actor seem to ghost him (not replying to any message anymore)
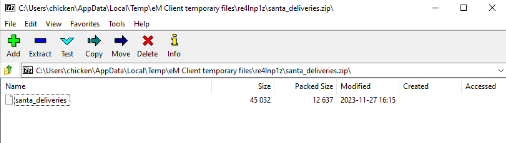
I extracted the attachment from an email and we can see that Elfin sent santa_deliveries binary to the threat actor.
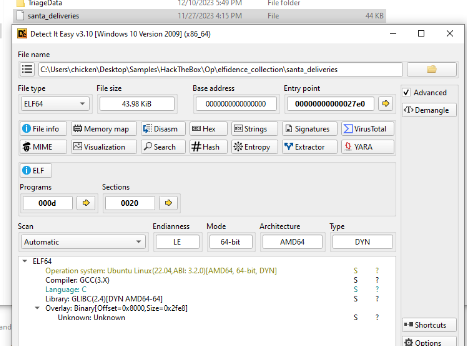
It is ELF binary and compiled with GCC so to understand what it does, we might need to decompile it.
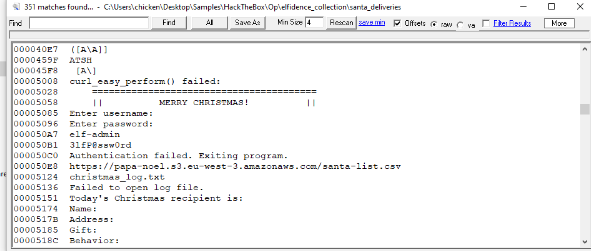
I ran strings on the binary to get a rough idea of what it might do, and we can see that it contains credential of "elf-admin" and exposed S3 bucket so this binary might be used in an automation of Santa gift delivery process.
definitelynotthegrinch@gmail.com
Task 3: When does the threat actor reach out to Elfin?
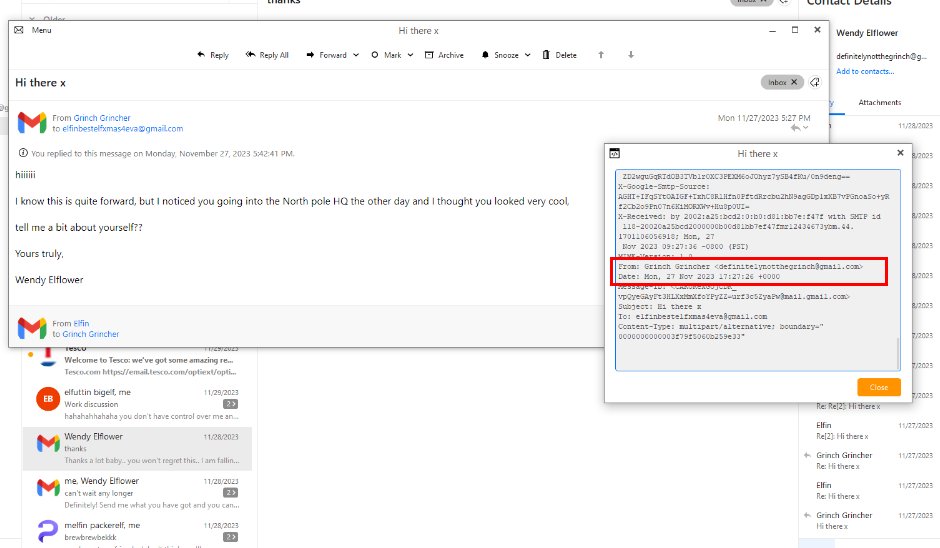
After determine who is the threat actor, We can go back to the first email sent to Elfin from the threat actor which we can see that at 2023-11-27 17:27:26, the threat actor still used the name "Grinch Grincher" to send email to Elfin.
The content of this email made it look like they have seen Elfin from the North Pole HQ, we can already see the inconsistency at the end that they introduced themselves as "Wendy Elflower" to Elfin.
2023-11-27 17:27:26
Task 4: What is the name of Elfins boss?
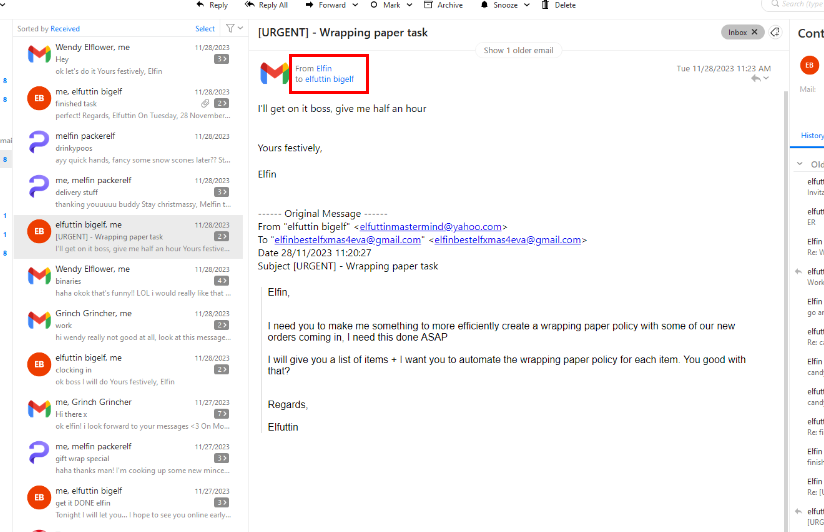
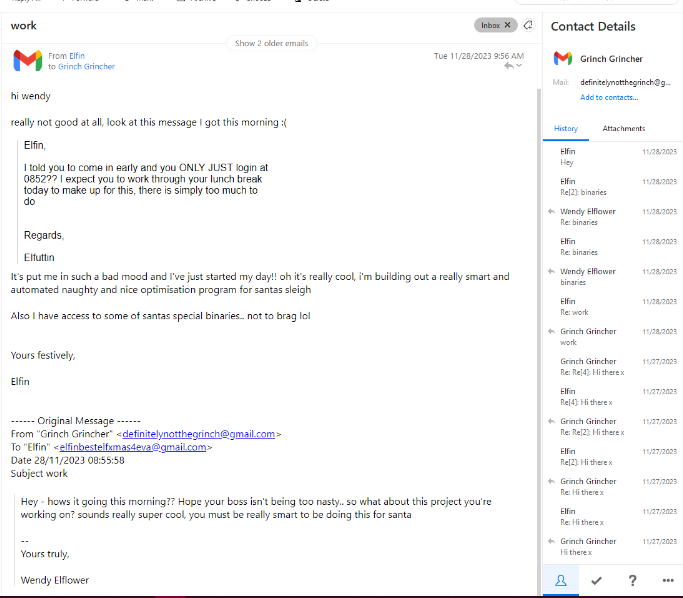
Inside the inbox, we can see that Elfin also had conversion with his boss "elfuttin bigelf" using an email as well and from the tone of the boss message sent to Elfin, I think we can understand how Elfin had joined the dark side at the end.
elfuttin bigelf
Task 5: What is the title of the email in which Elfin first mentions his access to Santas special files?
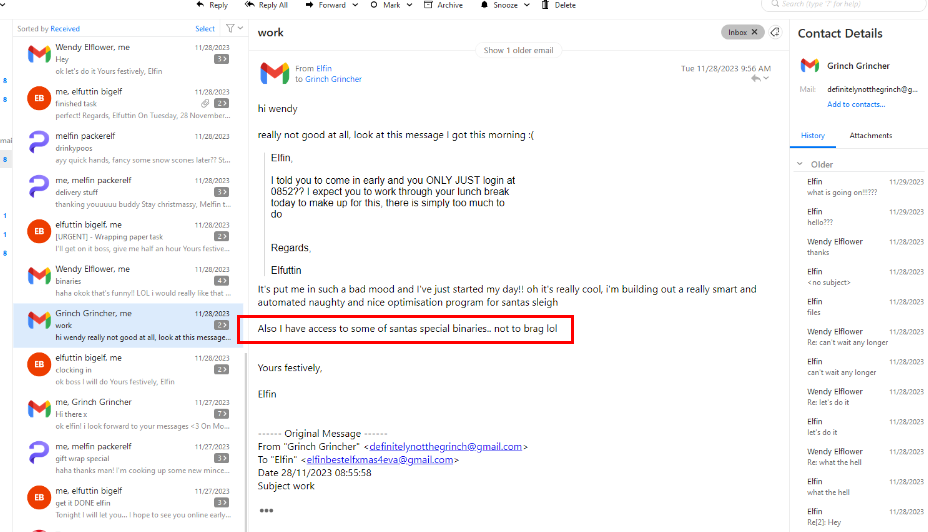
In one of the email, Elfin finally mentioned that he has access to some of santas special binaries to the threat actor after talking about work-related subject
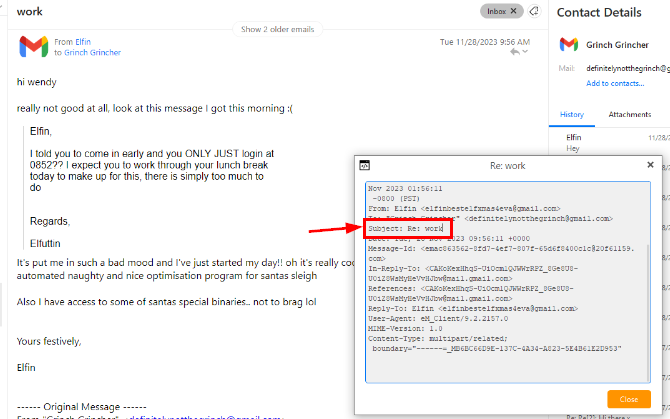
We can open the property of this email which we can see that it is a reply from the "Work" subject email sent by the threat actor to ask about the secret project that Elfin was working on.
Re: work
Task 6: The threat actor changes their name, what is the new name + the date of the first email Elfin receives with it?
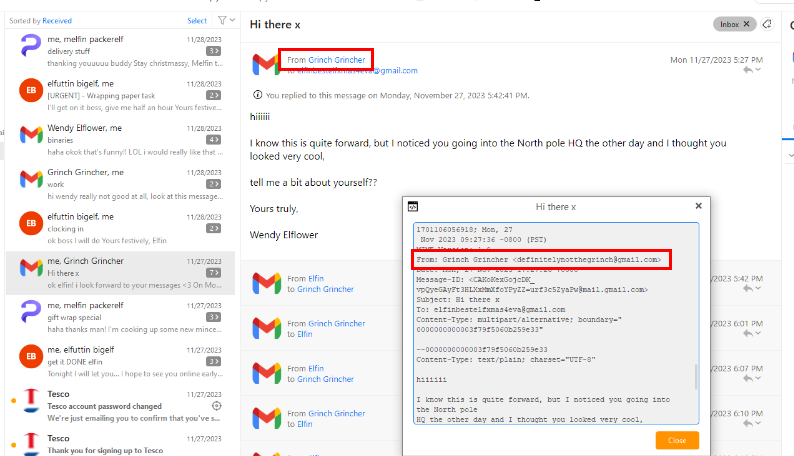
As we know that the threat actor used the different name on the email sender but introduced with the different name in the email body.
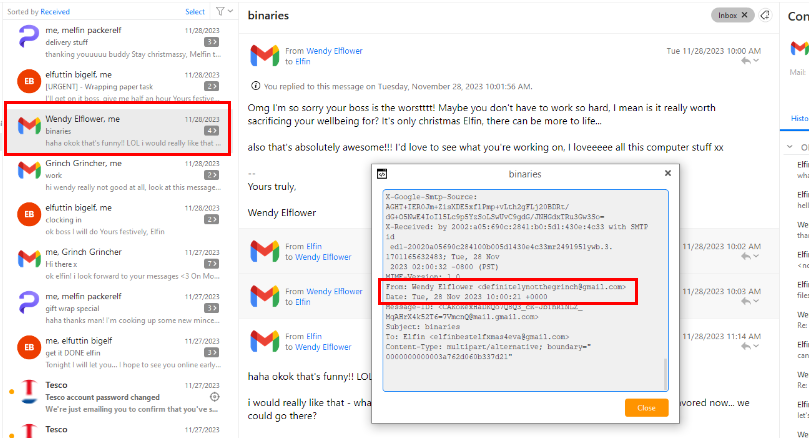
Which they finally changed in at 2023-11-28 10:00:21 when asking about special binaries that Elfin has access to.
wendy elflower, 2023-11-28 10:00:21
Task 7: What is the name of the bar that Elfin offers to meet the threat actor at?
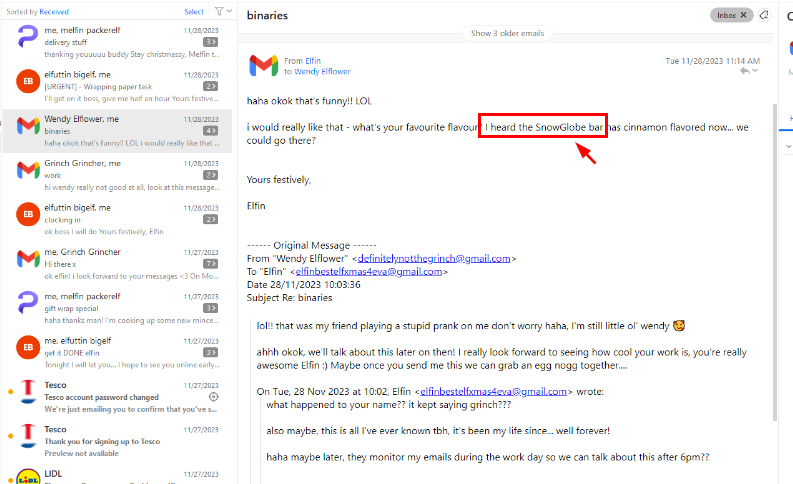
After knowing the existence of secret binary, the threat actor sent another mail to Elfin to question his work ethic, is is worth sacrificing his wellbeing for the work and they planed to have a meeting at SnowGlobe bar later.
SnowGlobe
Task 8: When does Elfin offer to send the secret files to the actor?
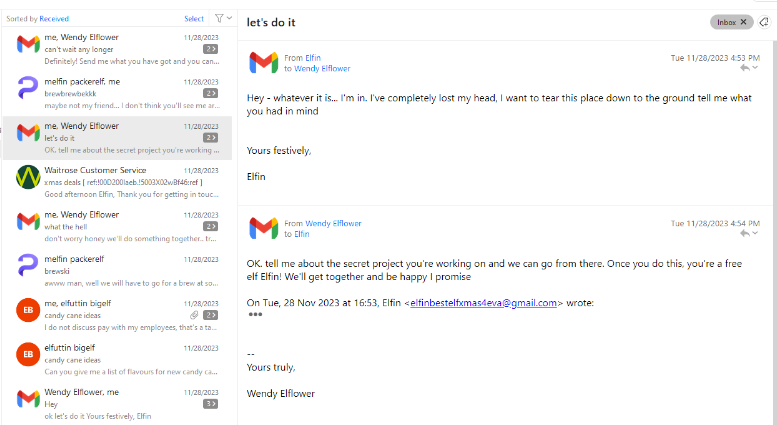
After giving himself in for the rage, Elfin sent another mail to the threat actor which they hold him to tell them more about the secret project Elfin had been working on.
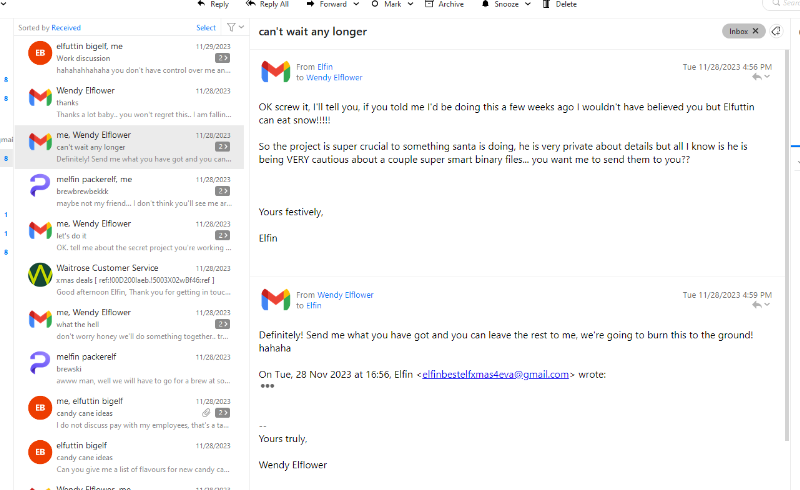
Elfin offered to send the binary to the threat actor which they agreed to let him send it to them
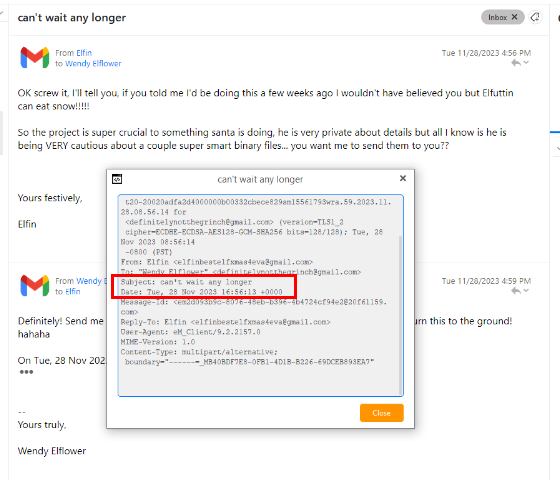
We can look at the email property (email header) to get the date header where the email was sent to the threat actor.
2023-11-28 16:56:13
Task 9: What is the search string for the first suspicious google search from Elfin? (Format: string)
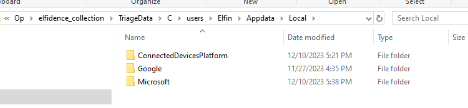
Now it is the time to look at the browser history and we can see that we have Google Chrome history for us here.
I used DB Browser for SQLite to open History file and use the following SQL Query to query url, title and datetime column from urls table and also convert datetime to UTC time and sort by lastvisittime
SELECT
url,
title,
datetime((last_visit_time / 1000000) - 11644473600, 'unixepoch') AS visit_time_utc
FROM urls
ORDER BY last_visit_time DESC;
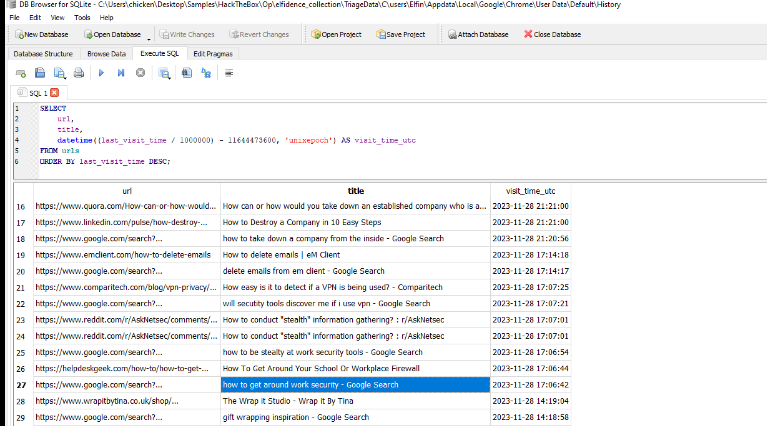
The result shows that after sending binary to the threat actor, Elfin searched on Google about how to get around work security, delete emails and how to destroy companies using Google Chrome.
how to get around work security
Task 10: What is the name of the author who wrote the article from the CIA field manual?
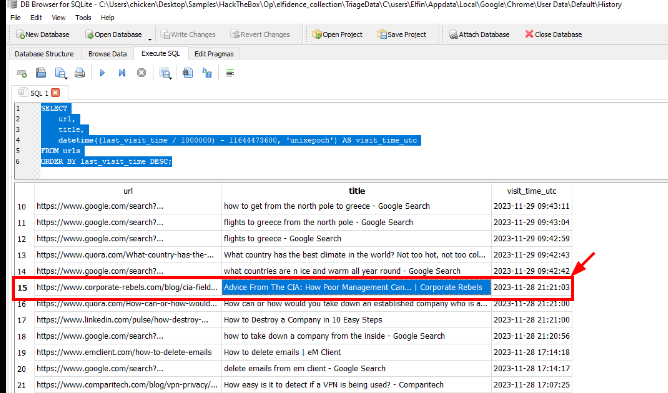
Elfin also accessed to CIA Manual about poor management can sabotage a workplace as well.
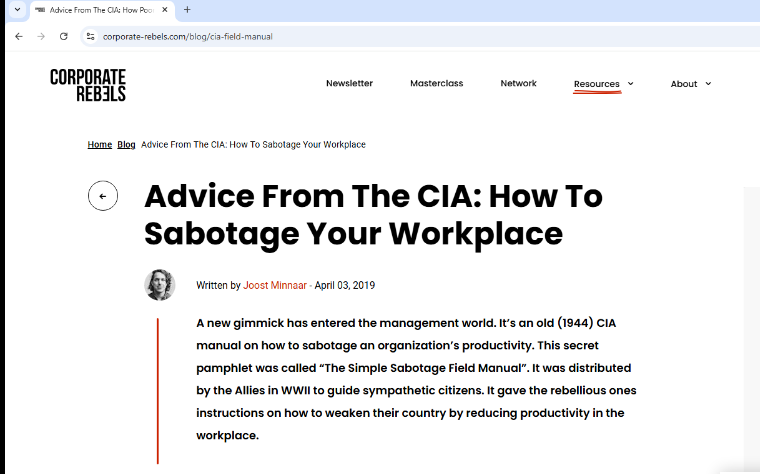
By following the URL, we can get the author who published this blog here.
Joost Minnaar
Task 11: What is the name of Santas secret file that Elfin sent to the actor?
santa_deliveries.zip
Task 12: According to the filesystem, what is the exact CreationTime of the secret file on Elfins host?
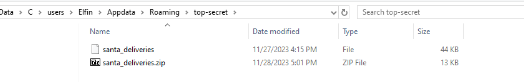
We also have the binary file which is located inside the top-secret folder here
There are 2 approaches that we can use to obtain answer of this question, let's go with the first approach first
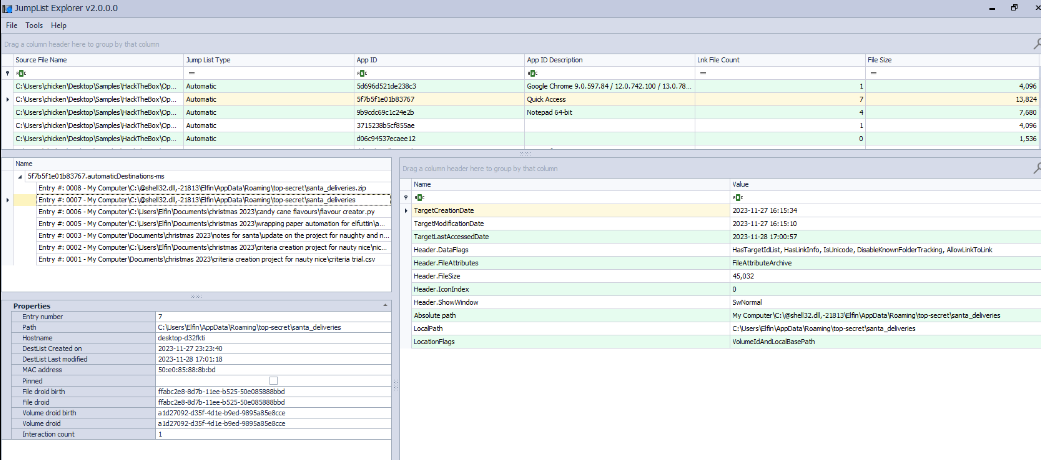
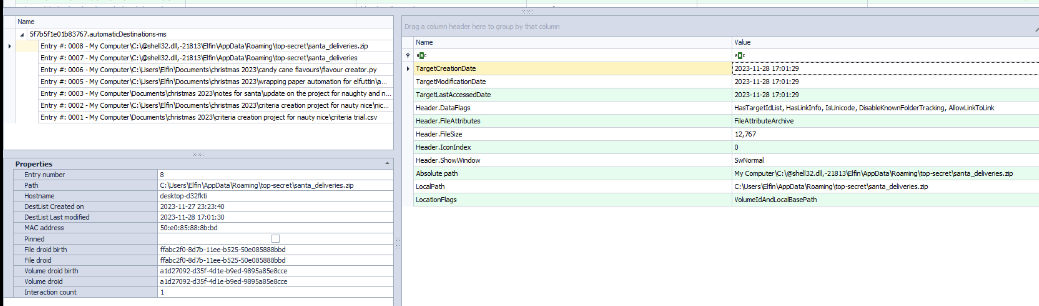
The first approach is to use JumpLists explorer to parse jumplists and we can see that the binary was created at 2023-11-27 16:15:34 and the zip file was created at 2023-11-28 17:01:29 just right before it was sent to the threat actor according to TargetCreationDate
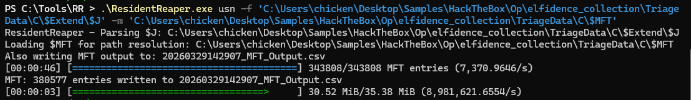
The second approach is obvious, we can either use MFT record or USN journal to find the answer which I will use my Resident Reaper tool to rapidly parsed both files together.
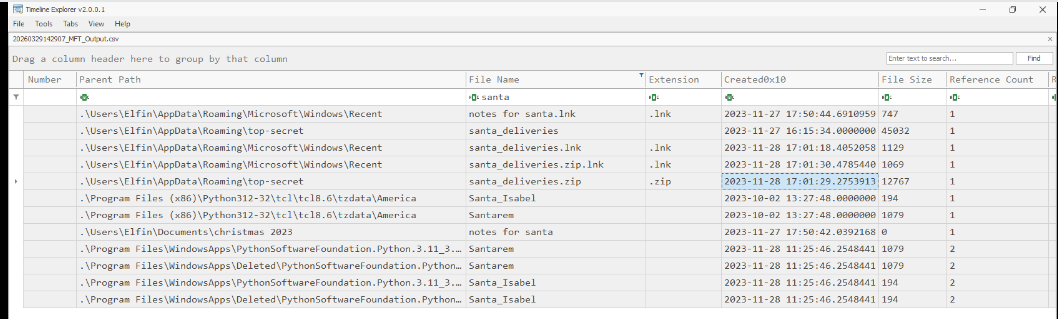
The Created0x01 column also contains the same timestamp we found from JumpLists so 2 different ways to approach the same conclusion
2023-11-28 17:01:29
Task 13: What is the full directory name that Elfin stored the file in?
C:\Users\Elfin\AppData\Roaming\top-secret
Task 14: Which country is Elfin trying to flee to after he exfiltrates the file?
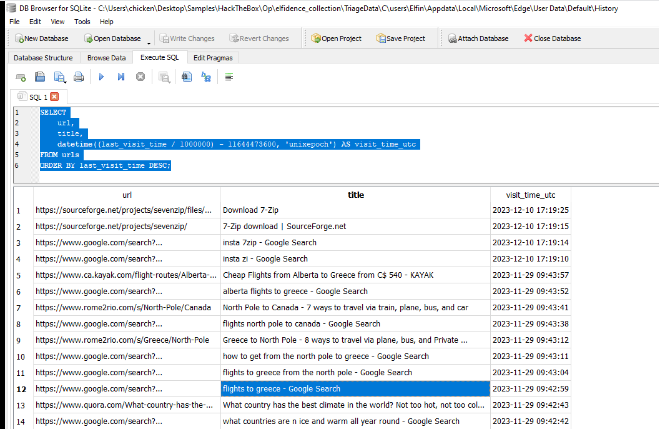
Elfin did search on Google about flights to Greece afterward.
Greece
Task 15: What is the email address of the apology letter the user (elfin) wrote out but didn’t send?
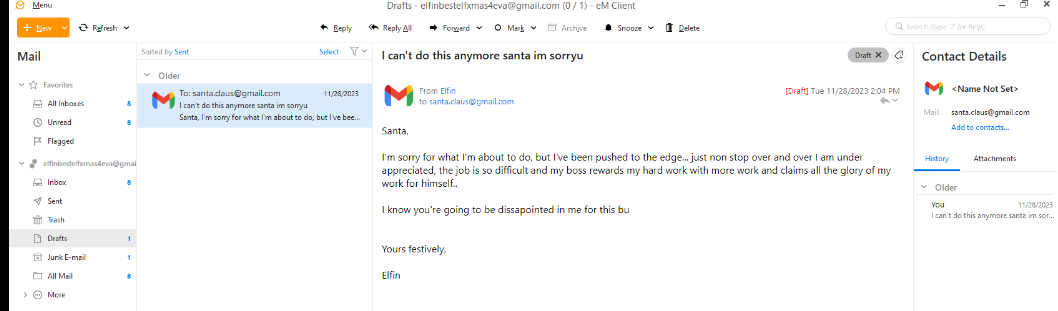
We can go look at the unfinished draft email which reveals an email address of the recipient that Elfin wanted to send his email to, which is a Santa Claus
santa.claus@gmail.com
Task 16: The head elf PixelPeppermint has requested any passwords of Elfins to assist in the investigation down the line. What’s the windows password of Elfin’s host?
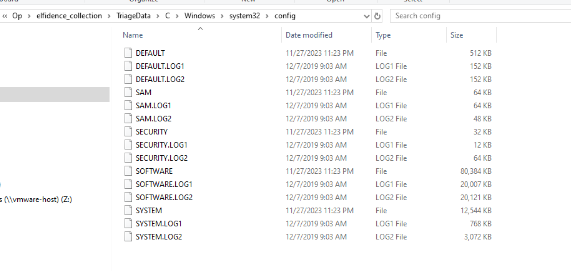
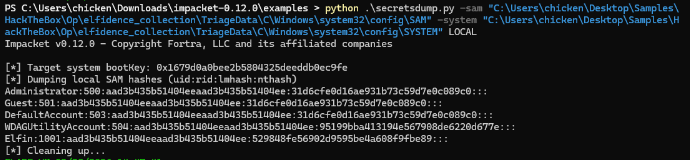
To recover Elfin password, we can use secretdump from impacket the dump NT hash of Elfin user like this.
Command:
python .\secretsdump.py -sam "C:\Users\chicken\Desktop\Samples\HackTheBox\Op\elfidence_collection\TriageData\C\Windows\system32\config\SAM" -system "C:\Users\chicken\Desktop\Samples\HackTheBox\Op\elfidence_collection\TriageData\C\Windows\system32\config\SYSTEM" LOCAL
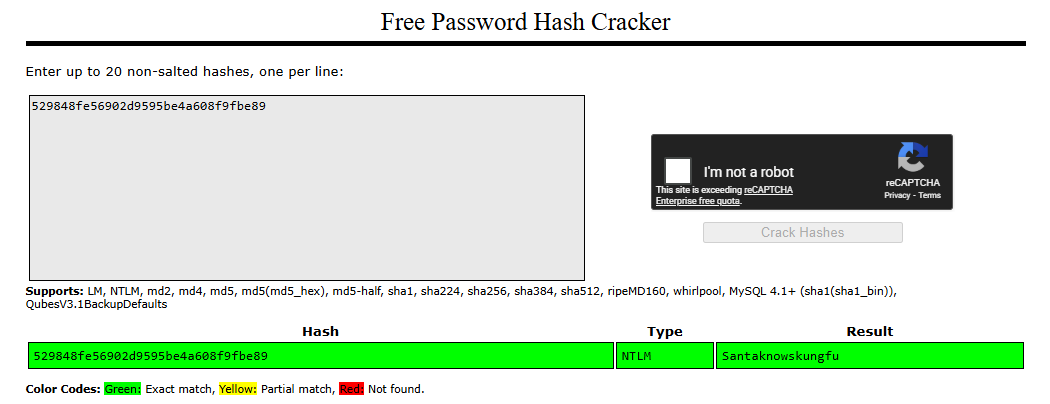
And then use public rainbow table service like crackstation to look up for the plaintext password which we can finally recover the password that was used by Elfin on this workstation here.
Santaknowskungfu
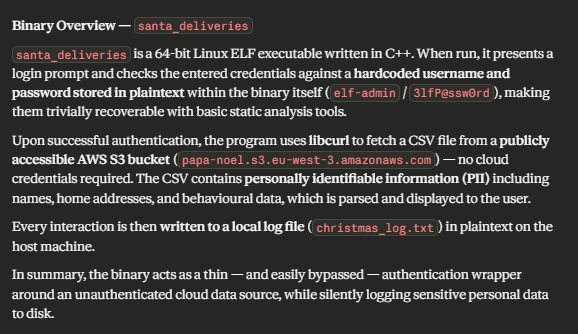
A little bit of extra here, the santa_deliveries contains hardcoded credential of elf-admin as we already discovered in strings and also fetch a file from public S3 bucket to retrieve information about kids and gifts before logging into a text file. this will help us in the OpTinselTrace-2 investigation later!

https://labs.hackthebox.com/achievement/sherlock/1438364/577